Zero Trust Architecture

Zero Trust
Cybersecure Policy Enforcement Point (PEP) | Encryption | Secure Authentication | Detailed Audit Logging
Zero Trust security models require that every request is explicitly authenticated, authorized, inspected, and logged, regardless of where it originates. Traditional network-based controls cannot provide this level of enforcement for modern, API-driven applications operating across hybrid, cloud, and on-prem environments. As organizations expose increasing numbers of services through APIs, they need a control point that can apply Zero Trust principles consistently at the application layer. An API Gateway fulfills this requirement by acting as the centralized policy enforcement point for all service interactions.
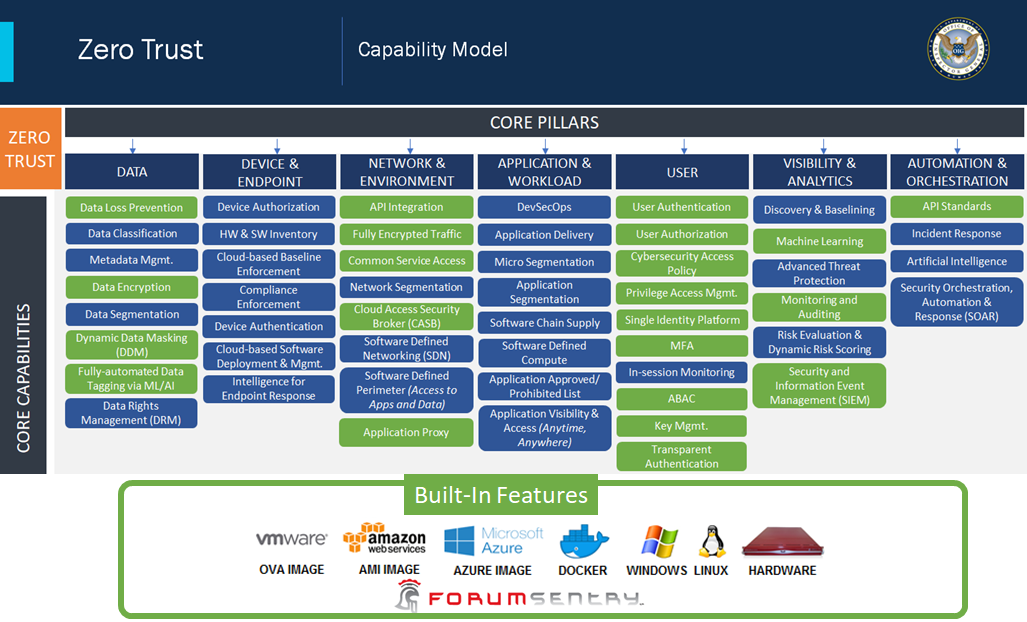
An API Gateway is essential to Zero Trust because it enforces identity-centric access control at the moment of every request. It validates user, service, and device identity, applies least-privilege authorization policies, and evaluates contextual signals such as source, scope, and behavior before allowing access. Without a Gateway, Zero Trust controls must be duplicated across individual services, leading to inconsistent enforcement, increased operational risk, and slower innovation. The Gateway provides a single, authoritative mechanism to implement Zero Trust policies uniformly across all APIs.
From a security and operational perspective, the API Gateway enables continuous verification, segmentation, and observability, which are foundational to Zero Trust. It prevents lateral movement by isolating services, limits blast radius through rate limiting and policy enforcement, and delivers centralized logging and auditing for compliance and threat detection. By embedding Zero Trust controls directly into the API access layer, organizations can secure hybrid and distributed environments without relying on fragile network perimeters. In this way, an API Gateway is not optional—it is a core architectural requirement for achieving Zero Trust at scale.
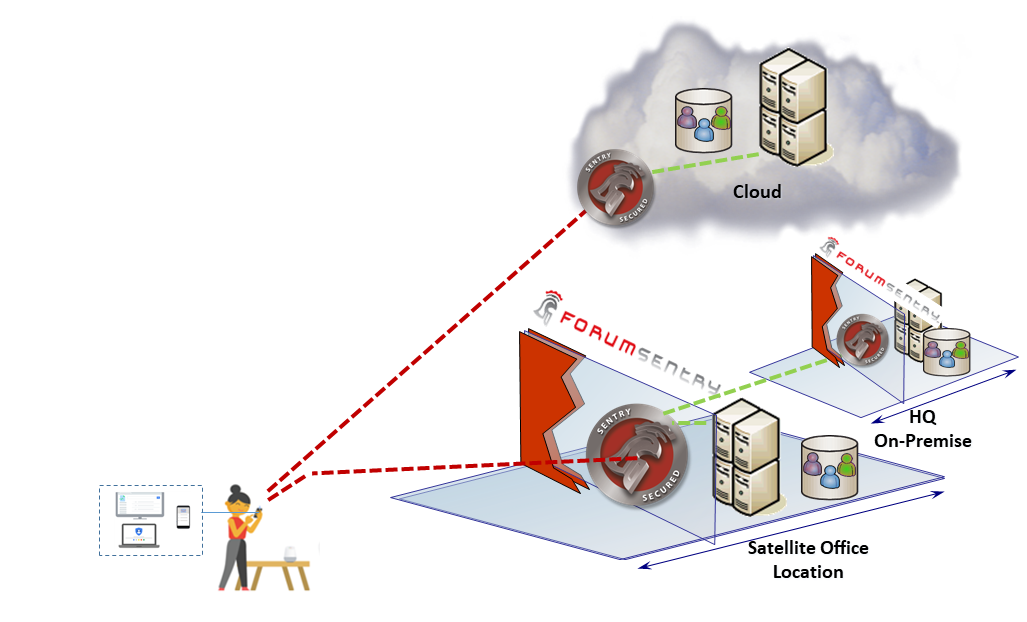
Achieving Zero Trust Architecture (ZTA) using Forum Sentry Policy Enforcement Points
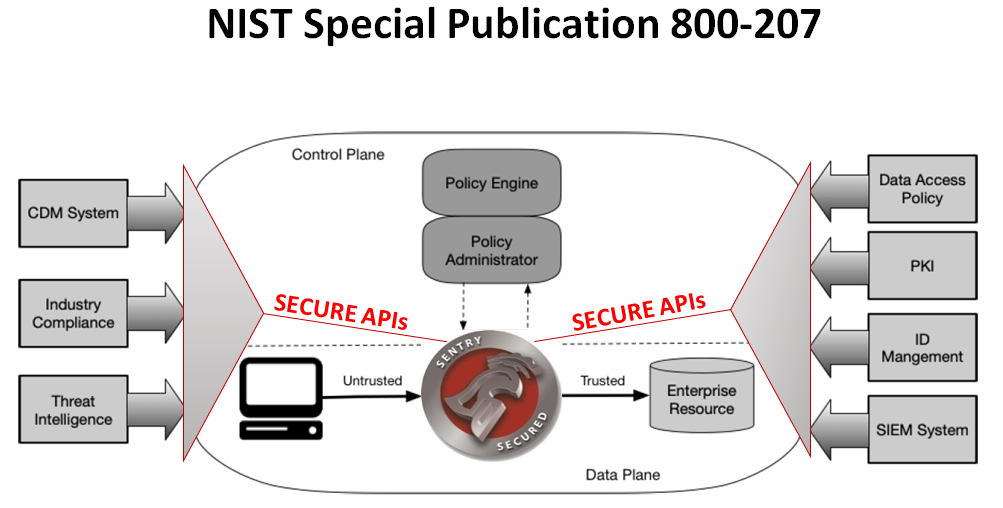
The National Institute for Standards and Technology has issued a special publication NIST SP 800-207 defining the architecture and concepts for deploying successful ZTA.
“Zero Trust Architecture is an end-to-end approach to network/data security that encompasses identity, credentials, access management, operations, endpoints, hosting environments, and the interconnecting infrastructure. Zero trust is an architectural approach that is focused on data protection.
…
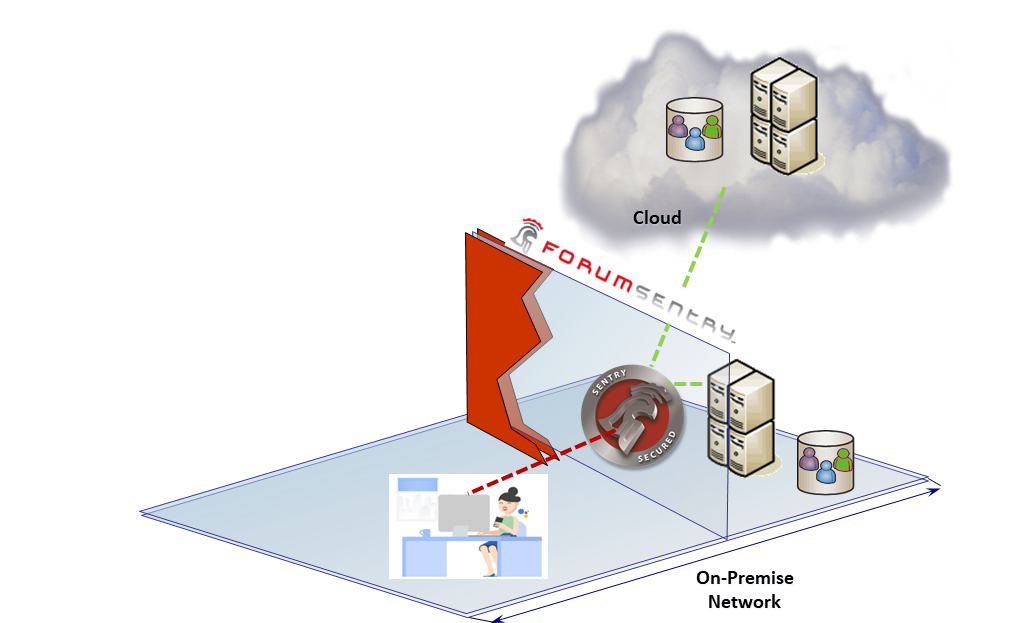
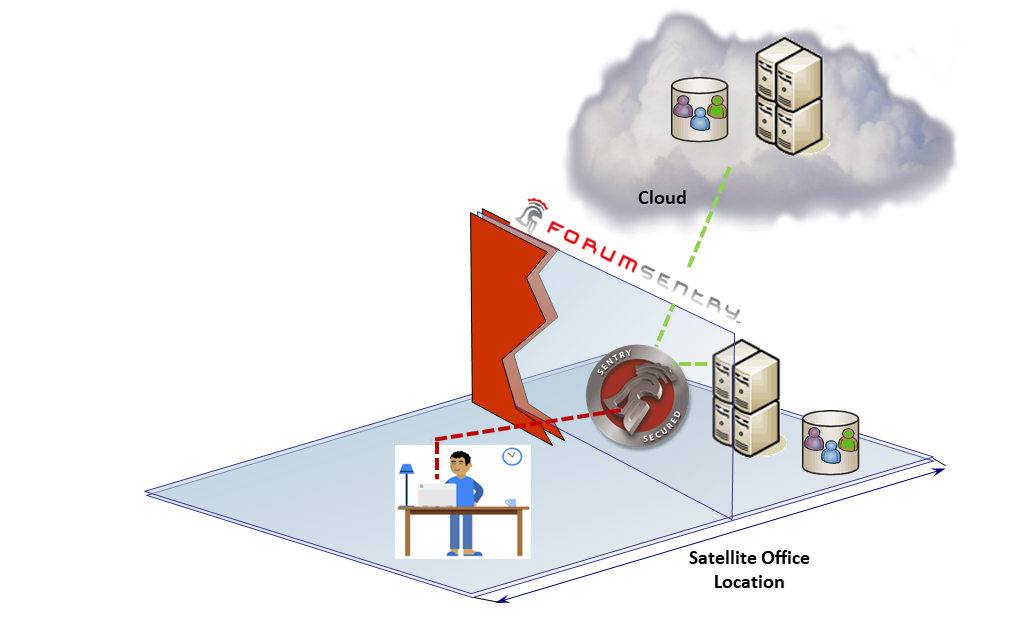
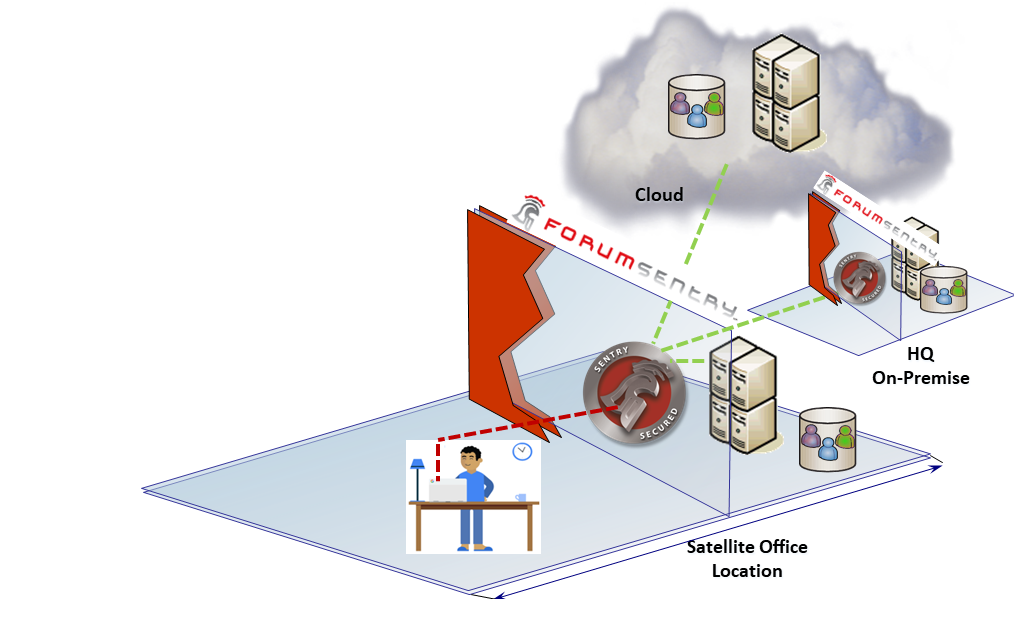
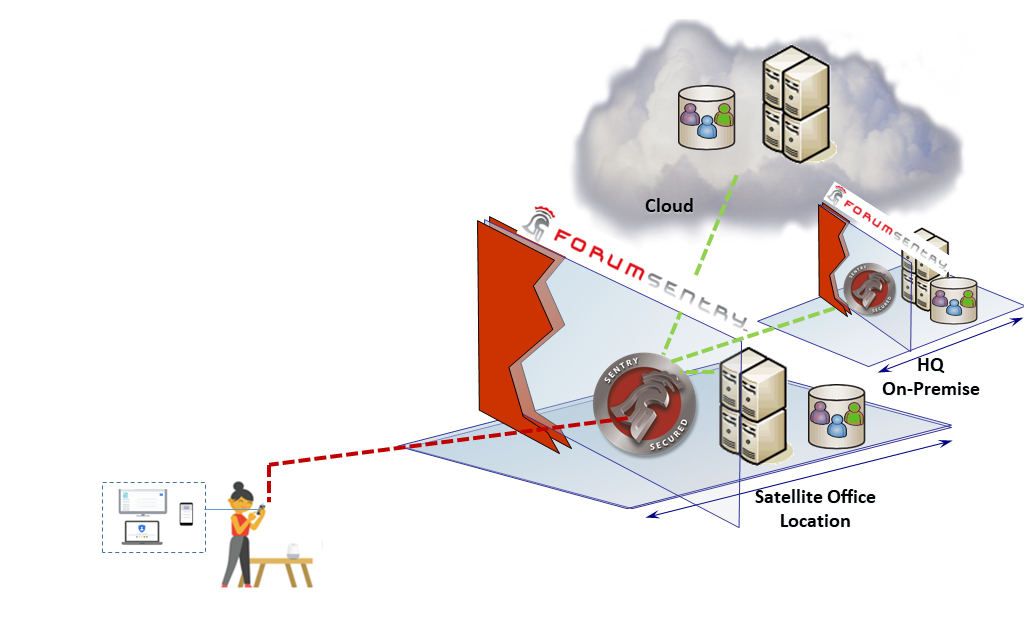
In Figure 1, a user or machine needs access to an enterprise resource. Access is granted through a 365 Policy Decision Point (PDP) and corresponding Policy Enforcement Point (PEP).
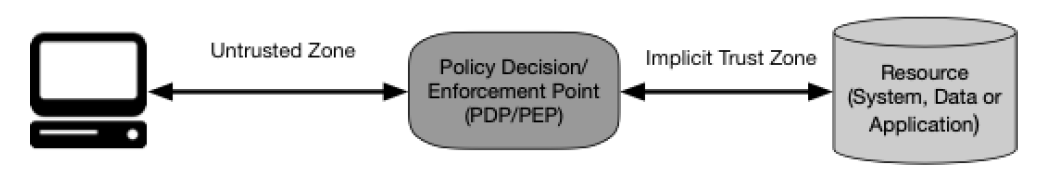
Risks of using insecure PEPs
While Policy Enforcement Points may claim that they provide access control, there are significant risks involved in deploying non cyber-hardened PEPs. This is because in a Zero Trust Architecture, the PEP itself is a critical decision point, and becomes by nature of the architecture itself, the target of attack.
Issues with non-secure PEPs:
- Open Architecture Without proper architecture design, open architecture solutions can be hacked or reverse engineered
- Not Hardened The PEP solution must be hardened against compromise. This includes a locked down, secure OS, self-health integrity checks, and inability to gain root or shell access.
- Agent Based PEP agents are software shims that are not designed to be cyber-hardened and thus are susceptible to compromise by attacks directly on the PEP solution, or on the underlying code hosting the agent.
- Developer Centric Agent and Adapter based PEPs rely on developer-centric security where repeatable security is difficult and case-by-case integrations increase risk.
- Limited Protocols Limits in the underlying technology of PEPs also limit the ability to include legacy systems in the ZTA architecture model, thus causing exceptions and other constraints to increase risk.
Forum Sentry Cyber-Secure PEP
Built-In Zero Trust Capabilities
- Transport Security
- Message Security
- Threat Mitigation
- Data Integrity Assurance
- Data Privacy Assurance
- Identity and SSO
- Data Translation
- Real-time Monitoring and Logging
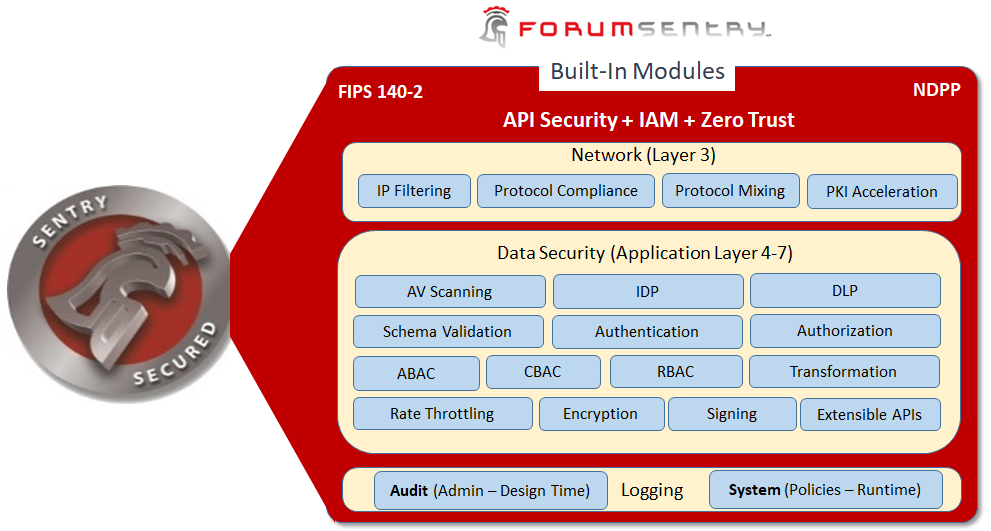
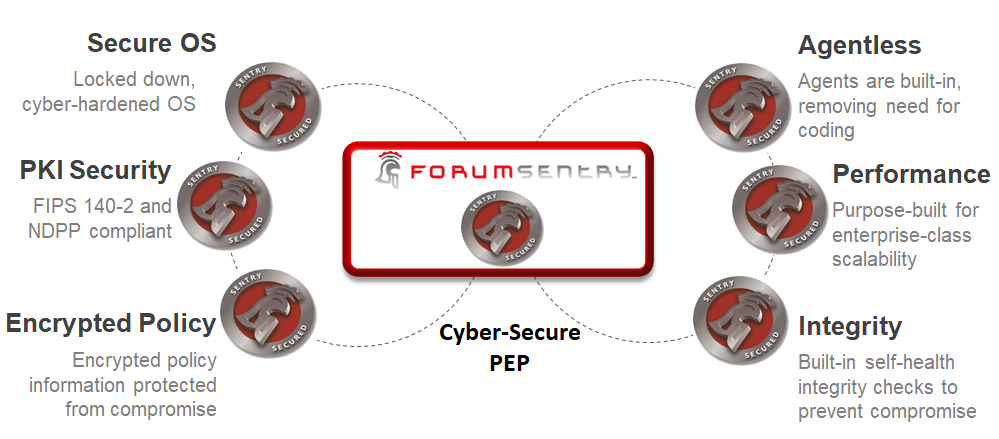
Forum Sentry has achieved FIPS 140-2 Level II, Common Criteria EAL NDPP, and DoD PKI certification. The product architecture is designed with tamper-proof self-health checks and Known Algorithm Test (KAT) validations to detect and prevent compromise. Forum Sentry provides integrated PKI, IDP, DLP, AV, and deep context data analysis engines that combine with the built-in identity, access control, authentication and authorization capability for dynamic and secure PEP enforcement. Furthermore, Forum Sentry captures transaction information bi-directionally into unique session identifiers for contextual logging, auditing, and real-time monitoring. Forum Sentry provides integration with AI machine learning for advanced predictive analytics of PEP message flows.
Example ZT Scenarios ( as demonstrated in ATARC labs )
Would you like to learn more?
Contact us for more information or to schedule a live demonstration.