Technical Papers
Technical Papers
White Paper: Best Practices for Deploying API Gateways
An API Security Gateway enables applications and services to be securely exposed, however, not all API Gateway technologies are created equal. In this white paper, you will learn best practices and common deployment scenarios of API Gateways and why they are an essential component of a secure, robust and scalable API infrastructure.

Top 10 API Threats and How to Prevent Them
Legacy cyber security technologies do nothing to stop API threats, because they were never designed to.
In Top 10 API Threats and How to Prevent Them, we will look at ten of today’s most common API hacks and how the Forum Sentry solution can stop them from penetrating the information border of your enterprises’ infrastructure.
Mobile Security and Authentication with an API Security Gateway
The Forum Sentry API Security Gateway provides mobile threat vector protection
In this white paper, you will learn how the Sentry API Security Gateway works seamlessly with MDM and provisioning solutions to provide the mobile gateway that combines cybersecurity with authentication and authorization all within a certified-secure product solution.
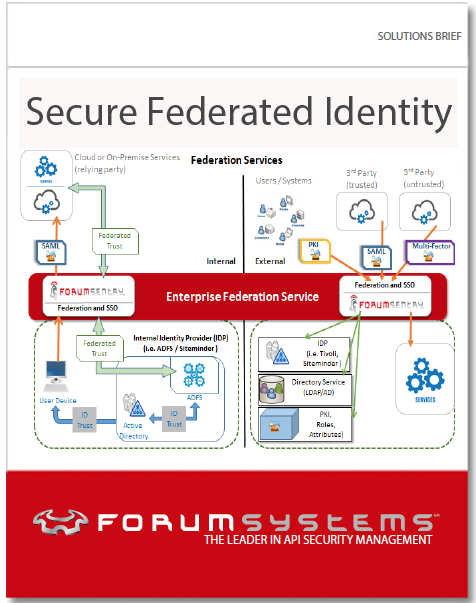
Solutions Brief: Secure Federated Identity
Identity Federation has become an essential business need to modernize capability and adapt to the evolving landscape of computing. The focus to achieving Identity Federation often revolves around product solutions that attempt to solve identity federation with agents, adapters, and rip-and-replace environment disruption. Forum Systems provides a different vision and proven capability to achieve secure identity federation. In this paper, we will discuss how to achieve identity federation in a landscape of existing IdM systems, repositories, directory services, and other user information stores by unifying these capabilities via a federation services architecture tier.

A Guide To Secure Web Services Using Forum Sentry To Achieve NIST SP 800-95
Forum Systems provides a FIPS 140-2 Level II compliant API Security Gateway technology that ensures compliance with NIST publication 800-95 for the securing of Web Services and API communications.
This document will specifically highlight how the Forum Sentry API Security Gateway provides the entire breadth of functionality to achieve all referenced aspects of NIST publication 800-95 and is the industry’s leading solution for NIST recommended security protection of deployed services.

White Paper: Reducing Application Cost and Risk through Centralized API Security
Implementing an agile and proper API security infrastructure is critical to protecting your apps and sensitive data. This white paper analyzes centralized and decentralized API security models, providing an in-depth look at the organizational impact and technical costs associated with each model.
White Paper: Using Forum Sentry to Achieve PCI Compliance
The Payment Card Industry Data Security Standard (PCI DSS) is a set of requirements designed to ensure that companies that store, process or transmit credit card information maintain a secure environment. Forum Sentry can provide the framework and infrastructure to enable PCI compliant transactions across a wide diversity of message formats and protocols.
White Paper: How to Implement Enterprise SAML SSO
One of SAML’s greatest benefits is Single Sign-On (SSO), the ability to enable users to securely access multiple applications with a single set of credentials, entered once. SAML enables users and organizations to conduct business faster and more efficiently. However, implementing SAML SSO can be challenging for an organization.
White Paper: Introduction to SAML
In today’s competitive business environment, enterprises are opening their applications for integration with their trading partners and users. One of the key requirements of a successful integration is granular access control to enterprise applications. Security Assertion Markup Language (SAML) is a proven and mature standard that provides such granular access control.
White Paper: How to Extend your Identity Management Systems to use OAuth
An enterprise’s identity management system is a critical component of its IT infrastructure. It is the primary service that is responsible for authenticating and authorizing an enterprise’s users and applications. Today, organizations need to extend their identity management system’s capabilities to authorize third party applications to access the organizations’ resources. The challenge is finding the time and resources to accomplish this.
White Paper: Enterprise Integration with Public Cloud Services using OAuth
Popular cloud service providers such as Google, Salesforce.com and Workday support REST and OAuth standards to enable enterprise integration. The challenge is coding, configuring and managing multiple applications with their respective cloud service providers.
White Paper: Cloud-based Enterprise Identity Management using OAuth
The basic model of authentication between a client and an application has evolved to keep up with the demands of mobile and cloud computing. A distributed architecture — where mobile clients request services from multiple protected systems — mandates Single Sign-On (SSO). OAuth provides a nimble SSO model to accommodate authentication for rapidly evolving mobile applications that consume services from a wide array of internal and external providers.
White Paper: Anatomy of a Web Services Attack
A Guide to Threats and Preventative Countermeasures